South Korea is world-famous for its blazing-fast internet, near-universal broadband coverage, and as a leader in digital innovation, hosting global tech brands like Hyundai, LG, and Samsung. But this very success has made the country a prime target for hackers and exposed how fragile its cybersecurity defenses remain.
The country is reeling from a string of high-profile hacks, affecting credit card companies, telecoms, tech startups, and government agencies, impacting vast swathes of the South Korean population. In each case, ministries and regulators appeared to scramble in parallel, sometimes deferring to one another rather than moving in unison.
Critics argue that South Korea’s cyber defenses are hindered by a fragmented system of government ministries and agencies, often resulting in slow and uncoordinated responses, per local media reports.
With no clear government agency acting as “first responder” following a cyberattack, the country’s cyber defenses are struggling to keep pace with its digital ambitions.
“The government’s approach to cybersecurity remains largely reactive, treating it as a crisis management issue rather than as critical national infrastructure,” Brian Pak, the chief executive of Seoul-based cybersecurity firm Theori, told TechCrunch.
Pak, who also serves as an advisor to SK Telecom’s parent company’s special committee on cybersecurity innovations, told TechCrunch that because government agencies tasked with cybersecurity work in silos, developing digital defenses and training skilled workers often get overlooked.
The country is also facing a severe shortage of skilled cybersecurity experts.
“[That’s] mainly because the current approach has held back workforce development. This lack of talent creates a vicious cycle. Without enough expertise, it’s impossible to build and maintain the proactive defenses needed to stay ahead of threats,” Pak continued.
Political deadlock has fostered a habit of seeking quick, obvious “quick fixes” after each crisis, said Pak, all the while the more challenging, long-term work of building digital resilience continues to be sidelined.
This year alone, there has been a major cybersecurity incident in South Korea almost every month, further mounting concerns over the resilience of South Korea’s digital infrastructure.
January 2025
- GS Retail, the operator of convenience stores and grocery markets across South Korea, confirmed a data breach that exposed the personal details of about 90,000 customers after its website was attacked between December 27 and January 4. The stolen information included names, birth dates, contact details, addresses, and email addresses.
February 2025
April and May 2025
- South Korea’s part-time job platform Albamon was hit by a hacking attack on April 30. The breach exposed the resumes of more than 20,000 users, including names, phone numbers, and email addresses.
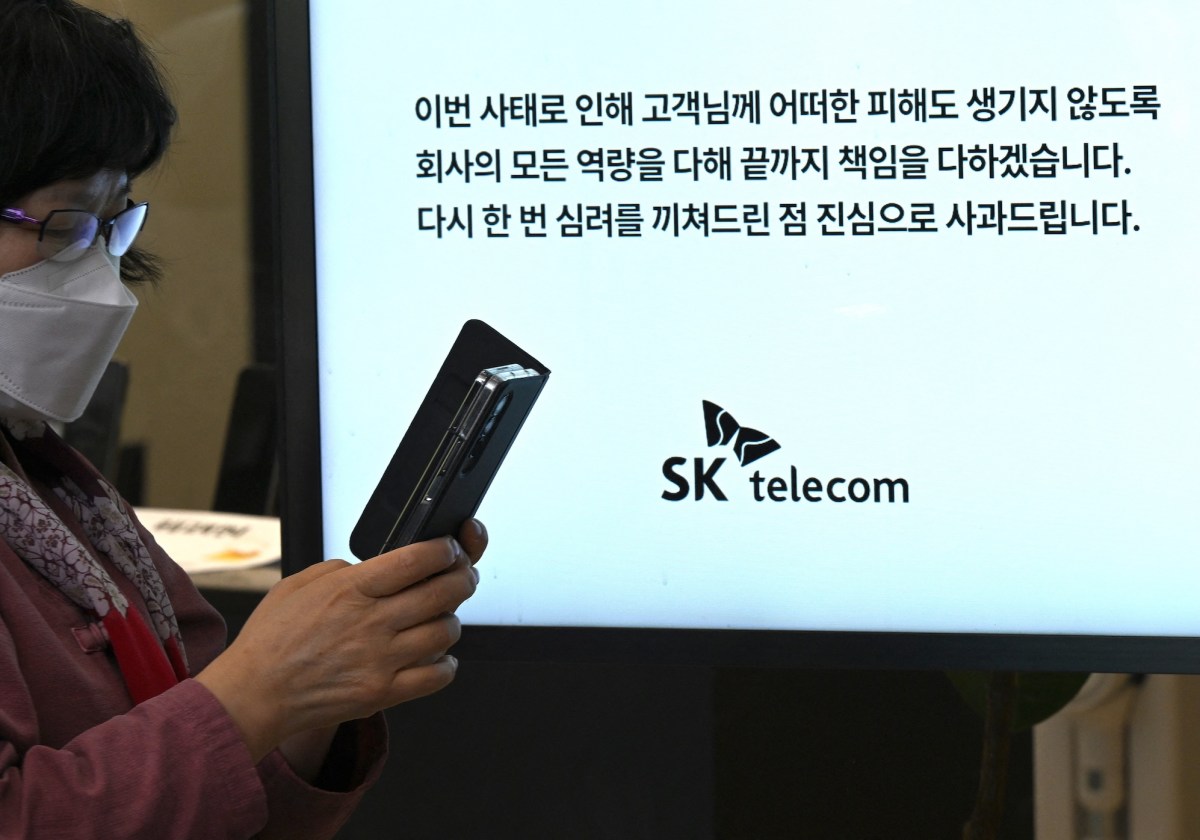
- In April, South Korea’s telecom giant SK Telecom was hit by a major cyberattack. Hackers stole the personal data of about 23 million customers — nearly half the country’s population. Much of the aftermath of the cyberattack lasted through May, in which millions of customers were offered a new SIM card following the breach.
June 2025
- Yes24, South Korea’s online ticketing and retail platform, was hit by a ransomware attack on June 9, which knocked its services offline. The disruption lasted for about four days, with the company back online by mid-June.
July 2025
- In July, the North Korea-linked Kimsuky group launched a cyberattack on South Korean organizations, including a defense-related institution, this time using AI-generated deepfake images.
- A North Korea-backed hacking group, Kimsuky, used AI-generated deepfake images in a July spear-phishing attempt against a South Korean military organization, according to Genians Security Center. The group has also targeted other South Korean institutions.
- Seoul Guarantee Insurance (SGI), a Korean financial institution, was hit by a ransomware attack around July 14, which disrupted its core systems. The incident knocked key services offline, including the issuing and verification of guarantees, leaving customers in limbo.
August 2025
- Yes24 faced a second ransomware attack in August 2025, which took its website and services offline for a few hours.
- Hackers broke into South Korean financial services company Lotte Card, which issues credit and debit cards, between July 22 and August. The breach exposed around 200GB of data and is believed to have affected roughly 3 million customers. The breach remained unnoticed for approximately 17 days, until the company discovered it on August 31.
- Welcome Financial: In August 2025, Welrix F&I, a lending arm of Welcome Financial Group, was hit by a ransomware attack. A Russian-linked hacking group claimed it stole over a terabyte of internal files, including sensitive customer data, and even leaked samples on the dark web.
- North Korea-linked hackers, believed to be the Kimsuky group, have been spying on foreign embassies in South Korea for months by disguising their attacks as routine diplomatic emails. According to Trellix, the campaign has been active since March and has targeted at least 19 embassies and foreign ministries in South Korea.
September 2025
- KT, one of South Korea’s biggest telecom operators, has reported a cyber breach that exposed subscriber data from more than 5,500 customers. The attack was linked to illegal “fake base stations” that tapped into KT’s network, enabling hackers to intercept mobile traffic, steal information like IMSI, IMEI, and phone numbers, and even make unauthorized micro-payments.
In light of the recent surge in hacking incidents, the South Korean Presidential Office’s National Security is stepping in to tighten defenses, pushing for a cross-ministerial effort that brings multiple agencies together in a coordinated, whole-of-government response.
In September 2025, the National Security Office announced that it would implement “comprehensive” cyber measures through an interagency plan, led by the South Korean president’s office. Regulators also signaled a legal change giving the government power to launch probes at the first sign of hacking — even if companies haven’t filed a report. Both steps aim to address the lack of a first responder that has long hindered South Korea’s cyber defenses.
But South Korea’s fragmented system leaves accountability weak, placing all authority in a presidential “control tower” could risk “politicization” and overreach, according to Pak.
A better path may be balance: a central body to set strategy and coordinate crises, paired with independent oversight to keep power in check. In a hybrid model, expert agencies like KISA would still handle the technical work — just with more straightforward rules and accountability, Pak told TechCrunch.
When reached for comment, a spokesperson for the South Korea’s Ministry of Science in ICT said the ministry, with KISA and other relevant agencies, is “committed to addressing increasingly sophisticated and advanced cyber threats.”
“We continue to work diligently to minimize potential harm to Korean businesses and the general public,” the spokesperson added.
This article was originally published on September 30.